Hello everybody,
I hope someone can help me with this problem. We use the following Camunda platform 8 in a Docker environment: GitHub - camunda/camunda-platform: Camunda Platform 8. We are currently building our own tasklist client. However, there are currently difficulties in accessing the tasks via GraphQL, since the Camunda task list and other Camunda components are protected by Keycloak. Unfortunately I don’t know how to proceed to authenticate myself correctly with Keycloak and to be able to make requests to the underlying API.
Through the Keycloak token endpoint (/auth/realms/camunda-platform/protocol/openid-connect/token) I can already get a bearer token from Keycloak. However, I still can’t make queries to the GraphQL endpoint of the tasklist with this token in the authorization header. Whenever this is attempted, a login HTML page is returned to me by Keycloak, regardless of which bearer token is used, or if a bearer token is used at all. On the contrary, the original camunda task list client works after manual authentication in the browser. However, we cannot reproduce this with any other client like Postman for example.
Feel free to ask additional questions.
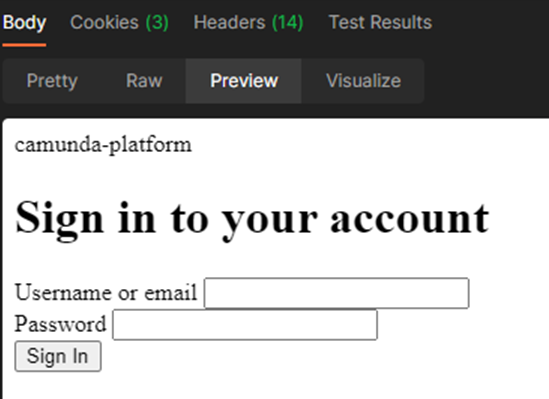
This is the default response of my queries to the graphql endpoint.
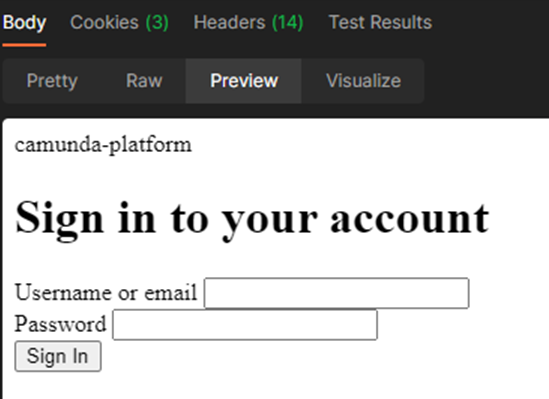
I use these keys with their corresponding values for obtaining the token.
var urlencoded = new URLSearchParams();
urlencoded.append(“client_id”, “tasklist-api”);
urlencoded.append(“grant_type”, “password”);
urlencoded.append(“client_secret”, “myClientSecret…”);
urlencoded.append(“scope”, “openid”);
urlencoded.append(“username”, “myUsername”);
urlencoded.append(“password”, “myPassword”);
Thanks in advance!
Hello everybody,
unfortunately the "/" character was missing at the end of the GraphQL tasklist Endpoint. We used something like localhost:8080/graphql and now we’re using something like localhost:8080/graphql/ and it’s now working as it should 
To figure out the mechanism how to properly authenticate with Keycloak we used Postman. There under Authorization there is the possibility to authenticate yourself using the oAuth2.0 protocol and to analyze the generated requests in the console.
I hope that whenever someone else runs into the same problem, they read this post.
Best wishes
Alwin Siemens
1 Like
Hey,
I’m trying to achieve the same thing. I can already get the bearer token from Keycloak instance, however when i’m trying to use it to access the graphql api i’m only seeing the redirect to the login page. As far as I can tell this happens because of the missing TASKLIST-SESSION cookie from the request.
I’m wondering how you managed to handle the cookie in the requests or if you managed to bypass it
Thanks!
Hey bulivlad,
Unfortunately, the problem hasn’t been completely solved for me either. After a while I noticed that I can now read the tasks, but I can’t claim any tasks. And that independent of a token. The error is then: “User is not authenticated”. The support thinks it has to do with the selfed managed variant. Something is not configured correctly with Keycloak.
The support said: the error is known and it is also being worked on. A patch should be available in August, which will then also bring the API queries from Tasklist in DockerCompose.
In principle, however, this error only affects DockerCompose; KeyCloak can be configured accordingly in the Kubernetes setup and then the API queries can also be implemented with self-managed.
Regarding your problem: I was missing a “/” at the end, and then I wasn’t redirected to the login page. I did this with Postman. I didn’t do anything else with the cookie for the time being, even though we noticed that Camunda’s Tasklist Client uses cookies.
I hope you can reproduce this on yours.
Best wishes
Alwin Siemens
Hi @alwin.siemens,
I wanted to follow up on this issue. Have you tried to use Identity JWT token to access Tasklist API?
This feature was released with the Camunda Platform 8.1.0-alpha3.
If yes, I’m curious if that worked as expected 
Best,
Aleksander
Hi @alwin.siemens
I am facing the same issue, Can you please help me on this?
I am also currently building our own tasklist client.
I got the token from Keycloak token endpoint (/auth/realms/camunda-platform/protocol/openid-connect/token), I still can’t make queries to the GraphQL endpoint of the tasklist with this token in the authorization header. Whenever this is attempted, a login HTML page is returned to me by Keycloak.
Here is the curl. also can you please provide what endpoint you are using, I am running on my local machine:
curl --location ‘http://localhost:8082/’
–header ‘Cookie: OPERATE-SESSION=B6AEA7285A0FA6C98C152A2EA46334BC; TASKLIST-SESSION=90EC903DCF32E8DE0283FEE8700C5AEC’
–data ‘’